QNX Hypervisor: Streamline Embedded Software Development
Modern embedded systems integrate diverse subsystems with unique resources, software, and hardware needs. Hypervisors improve hardware use, security, and scalability, enabling efficient development of complex, interoperable systems. They are especially valuable in automotive, industrial, aerospace, and medical electromechanical applications.
QNX® Hypervisor is an embedded virtualization solution with a microkernel architecture that enables multiple operating systems, including Android™, Linux®, and QNX, to safely operate on the same system-on-a-chip (SoC). This powerful solution offers virtual memory, CPUs, interrupt controllers, and pass-through, emulated, and para-virtualized devices, providing unparalleled scalability across CPU cores with extremely low jitter. With QNX Hypervisor, designers can share and isolate CPUs and devices (graphics, audio, etc.) between guests and the host without the fear of hitting hypervisor-based bottlenecks.
Accelerate Development
A Hypervisor built on QNX Software Development Platform (SDP) 8.0, accelerates development and saves time to build mixed criticality applications by first implementing algorithms on virtual machines. As automotive and industrial applications become more complex, software-defined architectures and digital twins are becoming a mainstay for developing the next generation of use cases
QNX Hypervisor 8.0 allows you to scale and deploy your systems efficiently while building complex embedded applications that interact and work together.
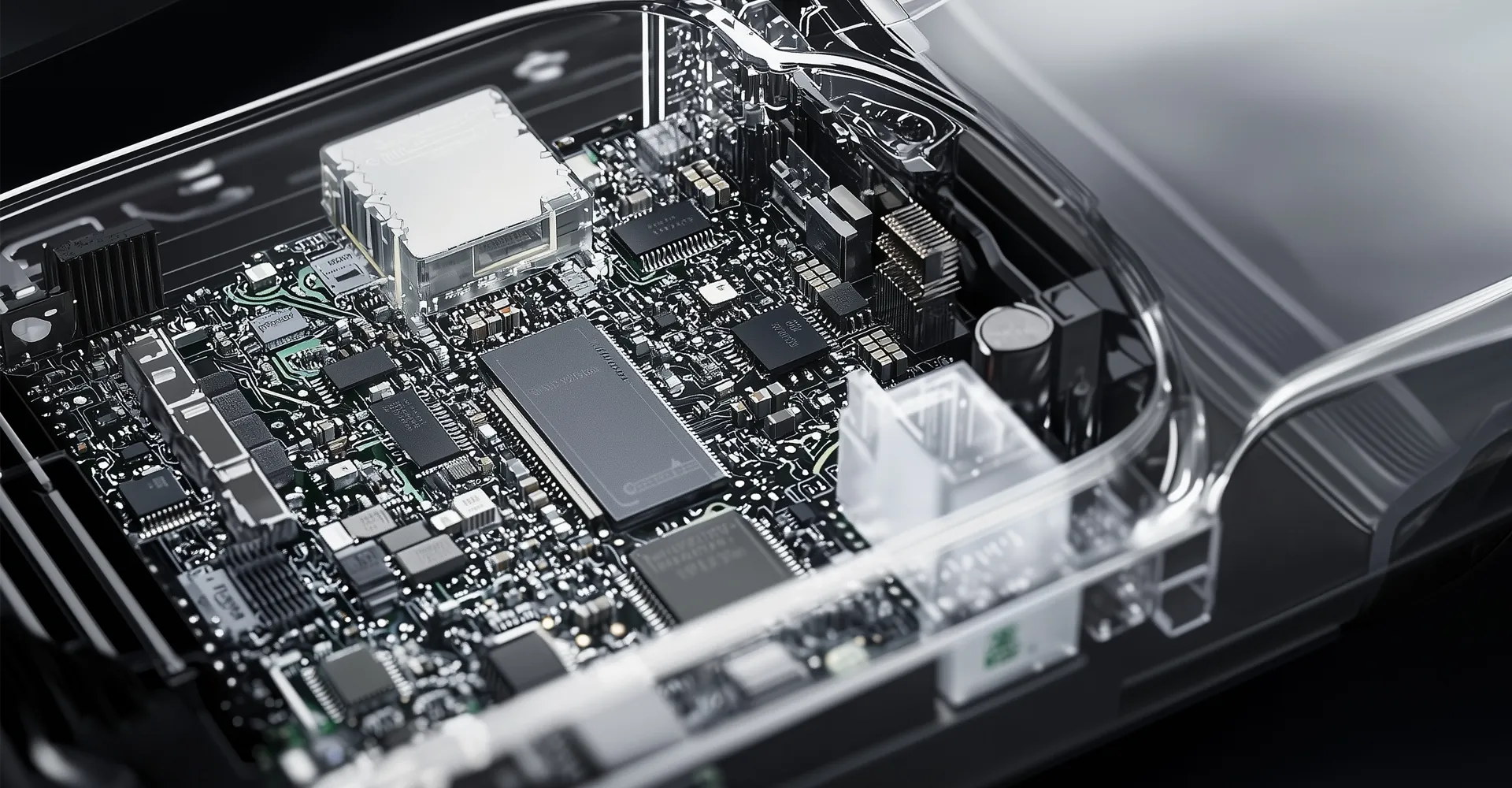
Optimize Resources with Single SoC Consolidation
Consolidate diverse embedded systems with different reliability and security requirements onto a single system on a chip (SoC) with the QNX® Hypervisor. Move unmodified legacy code onto the latest hardware simply by running it in an appropriately configured virtual machine. Just as easily, you can innovate with Android™ and Linux®. With guest OSs safely and securely contained in QNX Hypervisor virtual machines, you can run the apps and services you need with the OSs you choose.
With the QNX Hypervisor, you’ll implement the features your designs require, on the OSs you prefer, all while reducing system power consumption, the need for thermal dissipation, and the costs of both initial development and long-term ownership.

Improve Productivity, Security and Modularity with Isolated Virtualization
QNX Hypervisor offers a comprehensive virtualization solution, including virtual memory, CPUs, interrupt controllers, devices, and para-virtualized devices. Adding virtual machine management to the QNX® OS microkernel provides reliability and performance, proven for over 40 years in hundreds of millions of mission-critical systems.
QNX Hypervisor protects itself and your system from both internal faults and outside interference, including those of guests in virtual machines. If a guest attempts to overstep the boundaries you set, the hypervisor prevents them from completing the action. It also includes the SMMU manager service which works with hardware System Memory Management Units to ensure that Direct Memory Access devices are contained.
Collaborative and Familiar Development Environment
QNX Hypervisor 8.0 combines the advantages of a hybrid (Type 1 and Type 2) hypervisor offering ease and depth of development complexity, focusing on the developer and integrator first. QNX Hypervisor includes a virtual device developer’s API reference and a virtual device developer’s guide, complete with examples of virtual device source code you can use as models for developing your own virtual devices, including para-virtualized devices designed and built to the VIRTIO standards. QNX Hypervisor is fully API-compatible with the QNX OS API.
Develop non-safety and safety-critical applications on the same foundations, and continue working in the QNX Software Development Platform’s POSIX-compliant environment.

Versatile Virtualization Models
QNX Hypervisor leverages the latest ARMv8 and x86-64 virtualization extensions to offer versatile virtualization solutions with guest systems and the hypervisor itself contained and isolated. OSs and their applications can run as guests in thin virtual machines, limiting the hypervisor to handling events and exceptions. Guest systems can be supported by a full host environment running directly on the hypervisor (“bare metal”) that provides the backend services and removes the need for a complex service OS.
Devices in a QNX Hypervisor system can be physical devices (including pass-through devices) or virtual devices, including emulation and para-virtualized devices from our virtual device library. Diverse OSs share the same SoC and can share physical devices, reducing hardware costs.
TechInsights forecasts that in 2030, 90% of the vehicles produced will have at least one domain controller, zonal controller, or high-performance central computing unit. Hypervisors that offer rapid and reliable performance with modular design, such as the QNX Hypervisor 8.0, are thus vital to unlocking the potential of these platforms and making the software-defined vehicle a reality.
Ian Riches, VP of Global Automotive Practice, TechInsights
Learn More About QNX Hypervisor 8.0
QNX Hypervisor 8.0 is built as an extension of the proven QNX OS 8.0 microkernel design: QNX Hypervisor leverages the security, performance, real-time, and reliability of the trusted microkernel running as hypervisor host. QNX Hypervisor 8.0 leverages all the latest features of QNX SDP 8.0 delivering enhanced throughput, future-proofing architectures, and unparalleled scalability without compromising performance and jitter.
Virtualization Under Pressure

QNX Accelerate
Develop Mixed-Criticality systems with QNX Hypervisor in the Cloud
Build mission-critical embedded systems based on QNX® technology with QNX® Accelerate. By harnessing the agility, speed, and scale of the cloud, this initiative empowers developers in new ways—enabling better collaboration, increasing development efficiencies, and reducing time-to-market.
QNX OS for Safety and QNX Hypervisor are available globally on the Amazon Web Services (AWS) and Microsoft Azure marketplaces.
Related Products and Services




QNX Hypervisor FAQ
What is QNX Hypervisor 8.0 built on?
QNX Hypervisor 8.0 is built on QNX SDP 8.0 and therefore leverages the latest technology upgrades from our most recent foundational platform. QNX SDP 8.0 scales across CPU cores with negligible jitter, providing unparalleled performance, security and tools for your development.
What hardware does QNX Hypervisor 8.0 support?
QNX Hypervisor 8.0 is designed to run on QNX SDP 8.0 targets. It continues the QNX leadership in hybrid (Type1/Type2) virtualization designs by co-existing with advanced features of QNX SDP 8.0.
Is QNX Hypervisor already available and being adopted by the industry?
Yes, QNX Hypervisor 8.0 is now under general availability. It is a key component of QNX SDP 8.0 implementations with early access to OEMs and QNX partners.